Find every vulnerability before attackers do.
See what's exposed, fix what matters, and prove your security posture — all from one platform.
Free security check. No signup required. Results in 30 seconds.

Vuln Scanning
CVE detection
Attack Surface
Map exposure
App Security
Application checks
Attack Paths
Breach analysis
Phishing
Team awareness
Compliance
SOC 2 & ISO 27001
Code & Secrets
Repo scanning
Network
Internal scanning
Complete security coverage for teams from 5 to 5,000.
Security problems don't wait for your next audit.
new vulnerabilities published every year. How many are in your stack right now?
— NIST NVD
average cost of a data breach for US companies. Most breaches exploit known, fixable vulnerabilities.
— IBM Cost of a Data Breach Report, 2025
days to detect and contain a breach. Cybrove finds vulnerabilities in minutes.
— IBM Security, 2025
Whether you're securing your first product or managing hundreds of assets — if it's online, it has vulnerabilities. The only question is who finds them first.
One platform. Ten security modules. Complete coverage.
Find what's exposed. Fix what matters. Stay ahead of new threats — every module feeds into one Security Score that tells you exactly where you stand.
Vuln Scanning
CVE detection
Attack Surface
Map exposure
App Security
Application checks
Attack Paths
Breach analysis
Phishing
Team awareness
Compliance
SOC 2 & ISO 27001
Code & Secrets
Repo scanning
Network
Internal scanning
Vulnerability Scanning
CVE detection across your entire stack
Attack Surface Discovery
Map exposure automatically
App Security Testing
Application checks others skip
Attack Path Intelligence
See how breaches actually happen
Phishing Simulation
Test your team before attackers do
Compliance Reporting
SOC 2 & ISO 27001 in one click
Code & Secret Scanning
Find leaked credentials in repos
Network Security
Internal scanning via agent
Identity & OAuth Testing
Test auth flows and token security
Security Score
One number that tells you everything
Deep capabilities across every security layer.
Find every weakness. Map every asset.
Cybrove's dual-engine scanning combines vulnerability detection with automatic asset discovery. Know what you have and what's exposed — before an attacker maps it for you.
- Auto-discover subdomains, APIs, and forgotten assets
- Match CVEs against your actual technology stack
- Prioritize by exploitability, not just severity score
- Continuous monitoring catches new exposures in hours
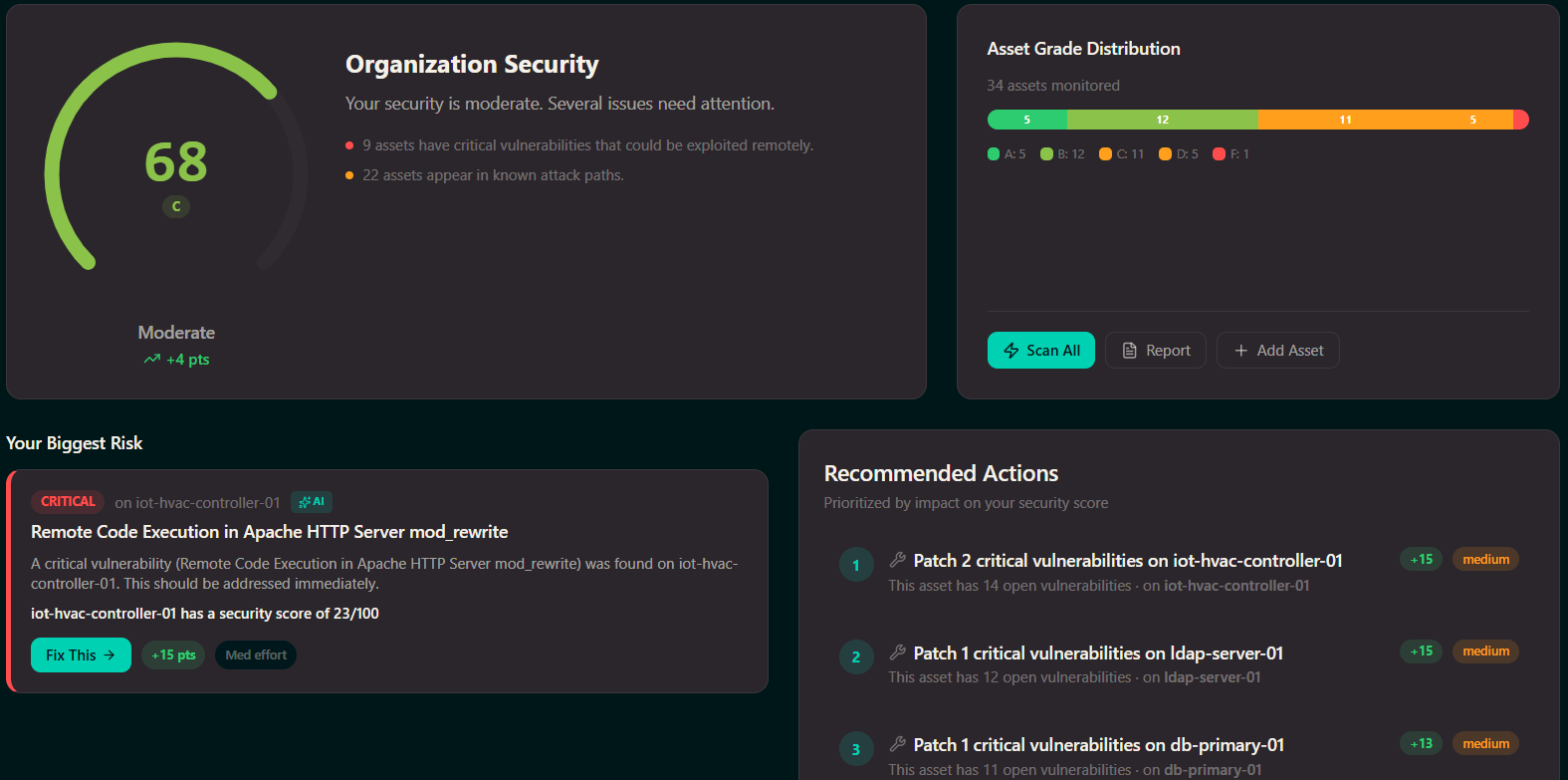
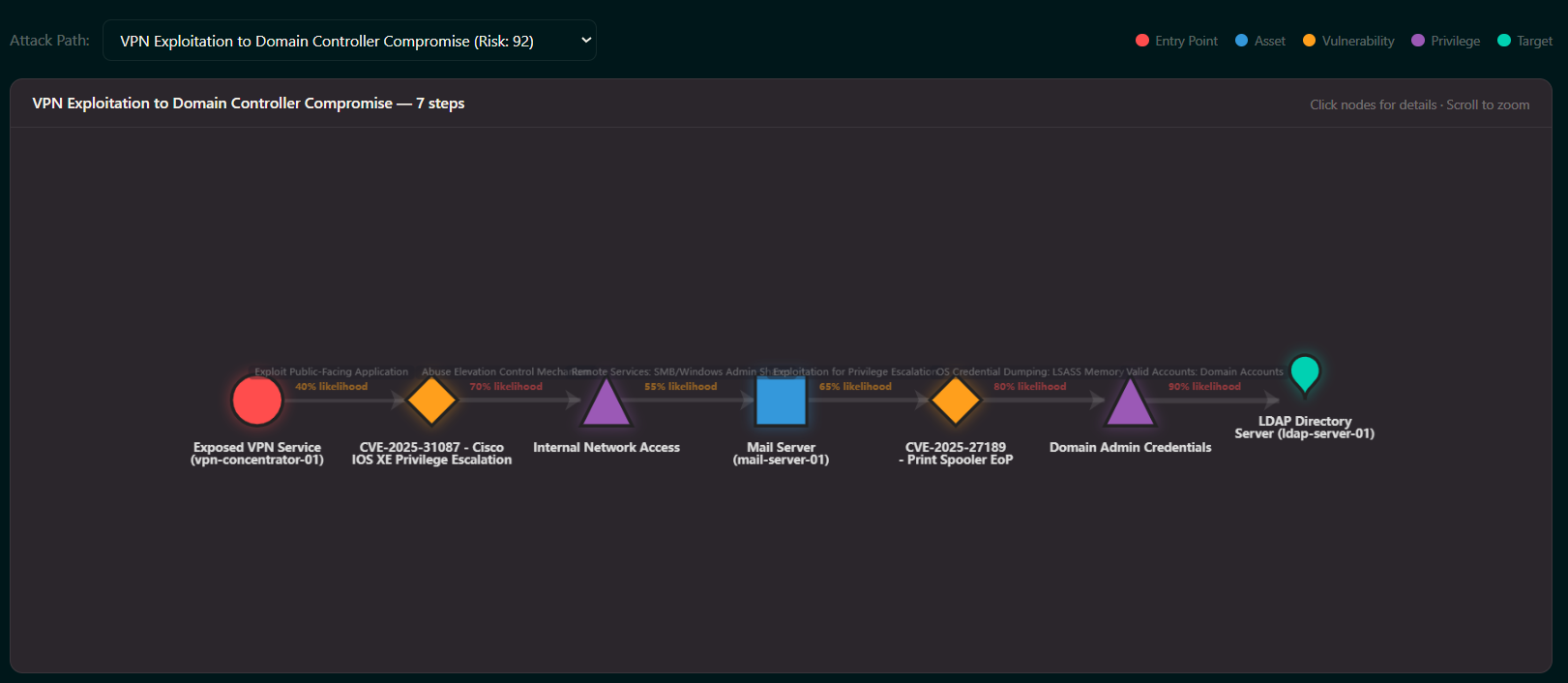
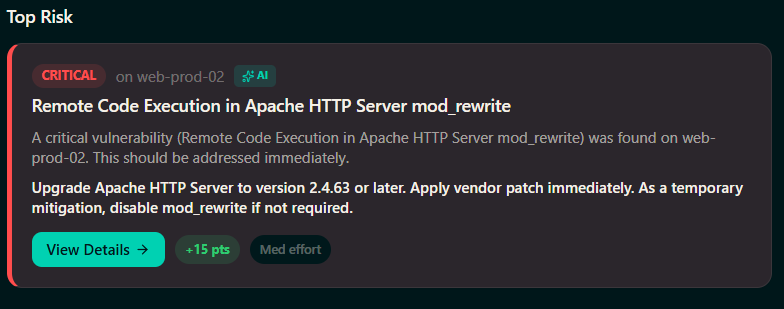
See exactly how a breach would happen.
A vulnerability list tells you what's wrong. An attack path shows you what an attacker would actually do. Cybrove chains vulnerabilities together to reveal the real-world paths to your most sensitive data.
- Visualize multi-step attack chains across your stack
- Identify which vulnerabilities are on a direct path to critical data
- Prioritize the fixes that break the most attack chains
- See before-and-after impact of every remediation
The checks traditional scanners skip.
Infrastructure scanners find server vulnerabilities but miss the application-level mistakes that cause most breaches. Cybrove tests your actual application logic — authentication flaws, broken access controls, injection vulnerabilities, and more.
- Test authentication, authorization, and session management
- Detect injection vulnerabilities (SQL, XSS, SSRF, and more)
- Check for broken access controls and data exposure
- Verify API security and input validation
Your perimeter is only as strong as your people.
The most common breach vector is not a zero-day exploit. It's a team member clicking a phishing link. Cybrove simulates real-world phishing campaigns so you can train your team before a real attack arrives.
- Launch realistic phishing simulations in minutes
- Track who clicks, who reports, and who needs training
- Automated follow-up training for at-risk team members
- Measure improvement over time with campaign analytics

Protected in under an hour.
No implementation consultants. No complex integrations. No security degree required.
Add your assets
Enter your domains, connect your GitHub repos, and add any IP ranges. Cybrove auto-discovers subdomains and related infrastructure.
Run your first security check
Choose Quick (5 min), Standard (30 min), or Deep (1-2 hrs). Every check runs all active modules across your entire attack surface.
See what needs fixing
Results prioritized by risk and grouped by action. Every finding explains what's wrong, why it matters, and exactly how to fix it.
Fix, verify, improve
Apply fixes. Re-check to confirm they worked. Watch your Security Score climb. Continuous monitoring catches new vulnerabilities as they appear.
Security isn't a one-time check. It's a continuous cycle.
New vulnerabilities are published daily. Your infrastructure changes with every deploy. Attackers don't stop probing. Neither does Cybrove.

Discover your attack surface
Cybrove automatically maps every domain, subdomain, API, and cloud asset connected to your organization. New assets are flagged the moment they appear.
Teams that take security seriously use Cybrove.
“We consolidated three security tools into Cybrove and went from a D to an A in two weeks. The board finally has a number they understand.”
CTO
B2B SaaS (50 employees)
“The plain language reports changed everything. Our devs actually read the findings now and fix them the same day.”
VP Engineering
Fintech startup
“The attack path analysis showed us the real danger wasn't a critical CVE — it was a medium misconfiguration sitting on a direct path to our database.”
Security Lead
Healthcare tech (200 employees)
“An enterprise customer needed proof of SOC 2 compliance. We generated the report in one click and closed the deal the following week.”
CEO
Series A B2B startup
Works with your tools
Designed for every stage of growth.
Whether you're securing your first product or managing compliance across business units — Cybrove scales with you.
Launch
Build trust from day one
- Vulnerability scanning and asset discovery for your first product
- Security Score and improvement roadmap from day one
- Prove your security posture to early customers and partners
Grow
Accelerate with confidence
- Attack path analysis reveals your real exposure across all assets
- Compliance evidence generation for SOC 2 and ISO 27001 audits
- Phishing simulation and executive-ready security reports
Scale
Command at scale
- Multi-team operations with role-based access and asset grouping
- Continuous compliance monitoring and automated audit preparation
- Full API access for CI/CD integration and custom workflows
Every breach starts with a vulnerability someone didn't find in time.
Check your free security score in 30 seconds. Or start your trial and get complete coverage.